In the hours following the attempted attack at the White House Correspondents’ Dinner, one question has quickly risen above all others:
How did this happen?
The annual gathering is not just another political event. It is one of the most tightly secured evenings in Washington, bringing together the President of the United States, senior administration officials, members of Congress, and high-profile media figures under a single roof.
Security at an event like this is layered, redundant, and designed with one objective in mind: prevent exactly what nearly occurred.
And yet, by all indications, those layers were tested in ways that are now forcing a hard reexamination of the system itself.
A Venue Under Lockdown—Or So It Seemed
The Washington Hilton, long the host of the Correspondents’ Dinner and the site of the attempted assassination on President Ronald Reagan, is no stranger to high-security operations. In the days leading up to the event, the venue is typically swept, secured, and placed under tight access control.
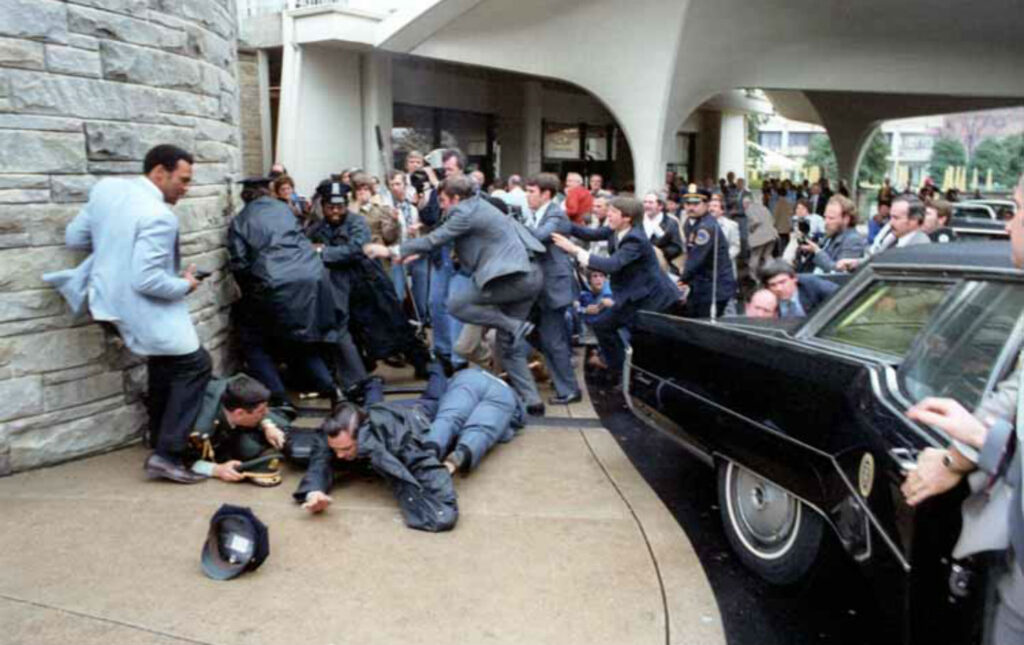
March 30, 1981: Ronald Reagan Is Shot at he exits the Washington Hilton.
Guest lists are vetted. Credentials are issued. Perimeters are established.
But security at an event like this does not rely on a single checkpoint. It relies on multiple rings of protection—outer, middle, and inner layers—each designed to detect and stop a threat before it can move closer to protected individuals.
What investigators are now examining is how a suspect was able to navigate those layers without being intercepted earlier in the process.
The Problem of Proximity
One of the most troubling aspects of the incident is not simply that an attack was attempted—but how close the suspect was able to get before the situation was neutralized.
Proximity is everything in protective operations.
The closer a threat gets, the fewer options remain. Reaction time shrinks. Risk increases. Outcomes become less predictable.
According to early findings, the suspect’s movements placed him within a zone that should have been tightly controlled. That fact alone is enough to trigger an internal review at the highest levels of federal security.
Because the system is not designed to respond at that stage. It is designed to prevent a threat from ever reaching it.

Screening, Access, and Assumptions
Security failures are rarely the result of a single breakdown. More often, they are the result of small gaps—missed signals, assumptions, or procedural blind spots—that align in ways no one anticipates.
Investigators are now expected to look closely at several key areas:
- Credentialing and access control: How was entry gained, and under what classification?
- Screening procedures: Were all standard protocols followed consistently?
- Movement within the venue: How closely were individuals monitored once inside secured areas?
Each of these layers is designed to function independently. When all are working properly, the system is extraordinarily difficult to breach.
When even one falters, the consequences can escalate quickly.
The Limits of Preparation
Even the most sophisticated security systems operate under constraints.
Events like the Correspondents’ Dinner involve large numbers of attendees, complex logistics, and an environment that blends formality with accessibility. Unlike a military installation, the setting cannot be completely sealed off from human unpredictability.
That tension—between openness and protection—is where vulnerabilities can emerge.
Security planners prepare for known risks. They model scenarios. They anticipate behaviors.
But they cannot eliminate uncertainty. And it is often within that uncertainty that incidents like this take shape.
A Rapid Response—But a Late One
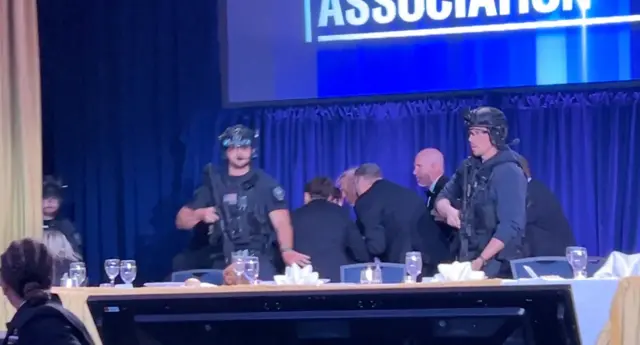
To the credit of the Secret Service and other security personnel, the response to the unfolding situation was immediate and decisive. The suspect was quickly confronted, and protective measures were enacted without hesitation.
That response likely prevented a far worse outcome. But response is not the same as prevention. And the fact that a response was required at all is what now demands scrutiny.
What Comes Next
Federal authorities are expected to conduct a full after-action review, examining every stage of the event—from pre-screening to on-site operations.
These reviews are standard after any security breach, but the stakes here are uniquely high. When the President is present, the margin for error is effectively zero. Any vulnerability—no matter how small—must be identified and addressed. Because the next time, the outcome may not hinge on response alone.
A System Under the Microscope
For now, the investigation continues, and many details remain under review. But the broader implication is already clear:
The system worked—but not where it mattered most.
A threat was identified and stopped. That is the baseline expectation.
The higher standard—the one the public assumes—is that the threat never gets close enough to matter. This time, it did.
And that is why the question is no longer just what happened. It is how.

Leave a Reply